Workload Security Webhook Example for Microsoft Teams
 Suggest changes
Suggest changes


Webhooks allow users to send alert notifications to various applications using a customized webhook channel. This page provides an example for setting up webhooks for Teams.

|
This page refers to third-party instructions, which are subject to change. Refer to the Teams documentation for the most up-to-date information. |
Teams Setup:
-
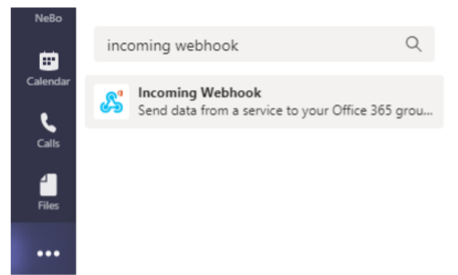
In Teams, select the kebab, and search for Incoming Webhook.
-
Select Add to a Team > Select a Team > Setup a Connector.
-
Copy the Webhook URL. You will need to paste this into the Workload Security webhook configuration.
Create Workload Security Teams Webhook:
-
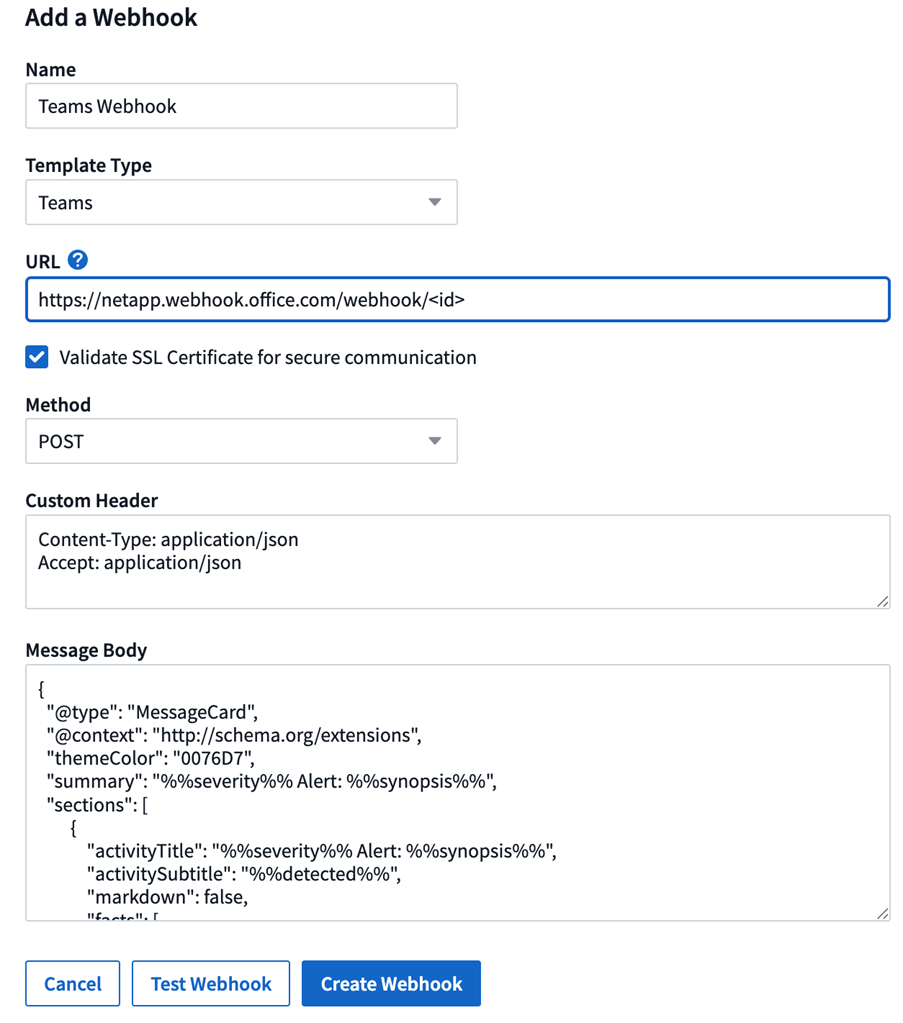
Navigate to Admin > Notifications and select the “Workload Security Webhooks tab. Select + Webhook to create a new webhook.
-
Give the webhook a meaningful Name.
-
In the Template Type drop-down, select Teams.
-
Paste the URL from above into the URL field.
Steps for creating Teams notification with Adaptive Card template
-
Replace the message body with the following template:
{ "type": "message", "attachments": [ { "contentType": "application/vnd.microsoft.card.adaptive", "content": { "$schema": "http://adaptivecards.io/schemas/adaptive-card.json", "type": "AdaptiveCard", "version": "1.2", "body": [ { "type": "TextBlock", "text": "%%severity%% Alert: %%synopsis%%", "wrap": true, "weight": "Bolder", "size": "Large" }, { "type": "TextBlock", "text": "%%detected%%", "wrap": true, "isSubtle": true, "spacing": "Small" }, { "type": "FactSet", "facts": [ { "title": "User", "value": "%%userName%%" }, { "title": "Attack/Abnormal Behavior", "value": "%%type%%" }, { "title": "Action taken", "value": "%%actionTaken%%" }, { "title": "Files encrypted", "value": "%%filesEncrypted%%" }, { "title": "Encrypted files suffix", "value": "%%encryptedFilesSuffix%%" }, { "title": "Files deleted", "value": "%%filesDeleted%%" }, { "title": "Activity Change Rate", "value": "%%changePercentage%%" }, { "title": "Severity", "value": "%%severity%%" }, { "title": "Status", "value": "%%status%%" }, { "title": "Notes", "value": "%%note%%" } ] } ], "actions": [ { "type": "Action.OpenUrl", "title": "View Details", "url": "https://%%cloudInsightsHostname%%/%%alertDetailsPageUrl%%" } ] } } ] } -
If you are using Power Automate Flows, query params in the URL are in encoded format. You must decode the URL before entering.
-
Click "Test Webhook" to ensure there are no errors.
-
Save the webhook.
Notifications via Webhook
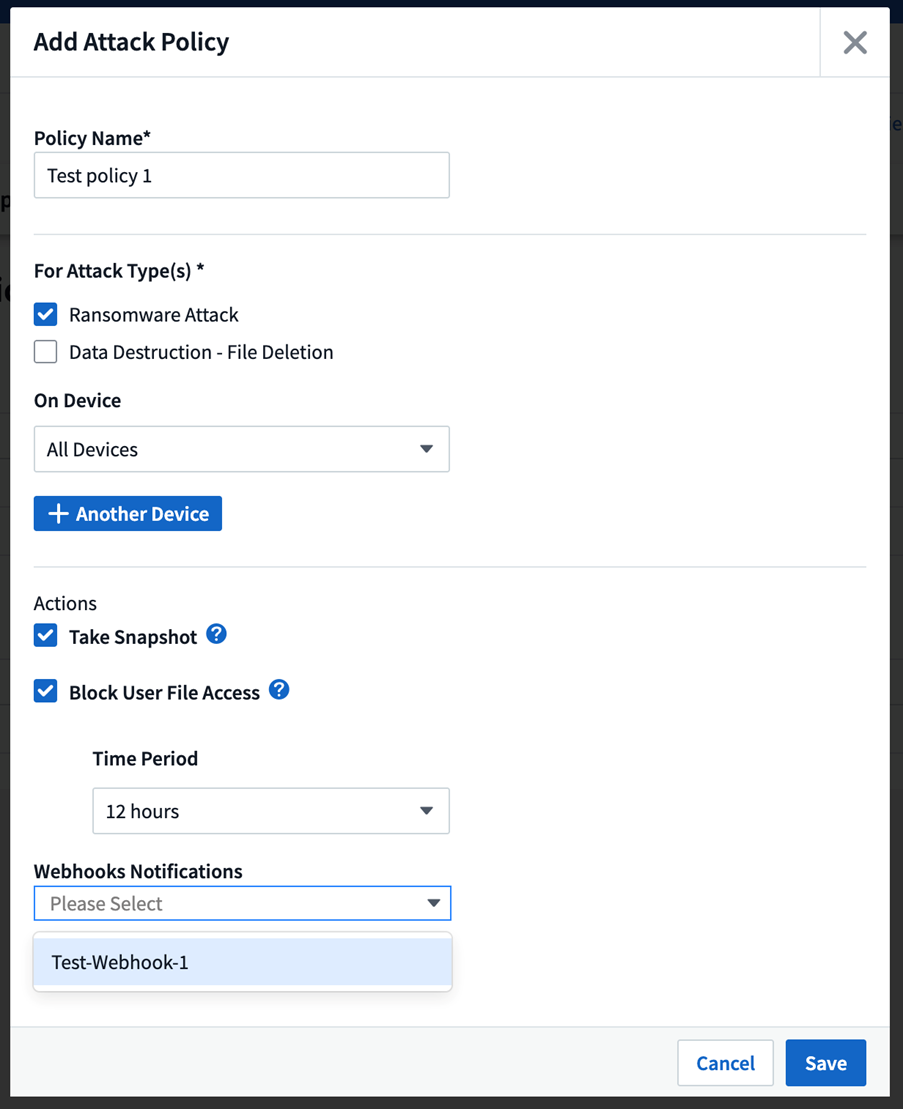
To notify on events via webhook, navigate to Workload Security > Policies. Select +Attack Policy or +Warning Policy.
-
Enter a meaningful policy name.
-
Select required Attack Type(s), Devices to which policy should be attached, and required Actions.
-
Under the Webhooks Notifications dropdown, select the required Teams webhooks. Save the policy.
Note: Webhooks can also be attached to existing policies by editing them.