StorageGRID中的策略和权限
 建议更改
建议更改


下面是StorageGRID S3中的策略和权限示例。
策略的结构
在StorageGRID中、组策略与AWS用户(IAM) S3服务策略相同。
StorageGRID中需要使用组策略。具有S3访问密钥但未分配给用户组或分配给组但策略未授予某些权限的用户将无法访问任何数据。
存储分段和组策略共享大多数相同的元素。策略以json格式构建、可使用生成 "AWS策略生成器"
所有策略都将定义效果、操作和资源。存储分段策略还将定义主体。
其*效果*是允许或拒绝请求。
负责人
-
仅适用于存储分段策略。
-
主体是指被授予或拒绝权限的帐户/用户。
-
可以定义为:
-
通配符"*"
"Principal":"*"
"Principal":{"AWS":"*"} -
租户中所有用户的租户ID (相当于AWS帐户)
"Principal": { "AWS": "27233906934684427525" } -
用户(存储分段所在租户的本地或联合用户、或网格中的其他租户)
"Principal": { "AWS": "arn:aws:iam::76233906934699427431:user/tenant1user1" }"Principal": { "AWS": "arn:aws:iam::27233906934684427525:federated-user/tenant2user1" } -
组(存储分段所在租户的本地或联合组、或网格中的其他租户)。
"Principal": { "AWS": "arn:aws:iam::76233906934699427431:group/DevOps" }"Principal": { "AWS": "arn:aws:iam::27233906934684427525:federated-group/Managers" }
-
“操作”是授予或拒绝给用户的一组S3操作。

|
对于组策略、用户需要执行S3:ListBucket"操作才能执行任何S3操作。 |
资源*是指被授予或拒绝对其执行操作的主体的一个或多个分段。(可选)策略操作的有效时间可以是一个*条件*。
JSON策略的格式如下所示:
{
"Statement": [
{
"Sid": "Custom name for this permission",
"Effect": "Allow or Deny",
"Principal": {
"AWS": [
"arn:aws:iam::tenant_ID::user/User_Name",
"arn:aws:iam::tenant_ID::federated-user/User_Name",
"arn:aws:iam::tenant_ID:group/Group_Name",
"arn:aws:iam::tenant_ID:federated-group/Group_Name",
"tenant_ID"
]
},
"Action": [
"s3:ListBucket",
"s3:Other_Action"
],
"Resource": [
"arn:aws:s3:::Example_Bucket",
"arn:aws:s3:::Example_Bucket/*"
],
}
]
}使用AWS策略生成器
AWS策略生成器是一个很好的工具、可帮助您获取具有正确格式的json代码以及您尝试实施的信息。
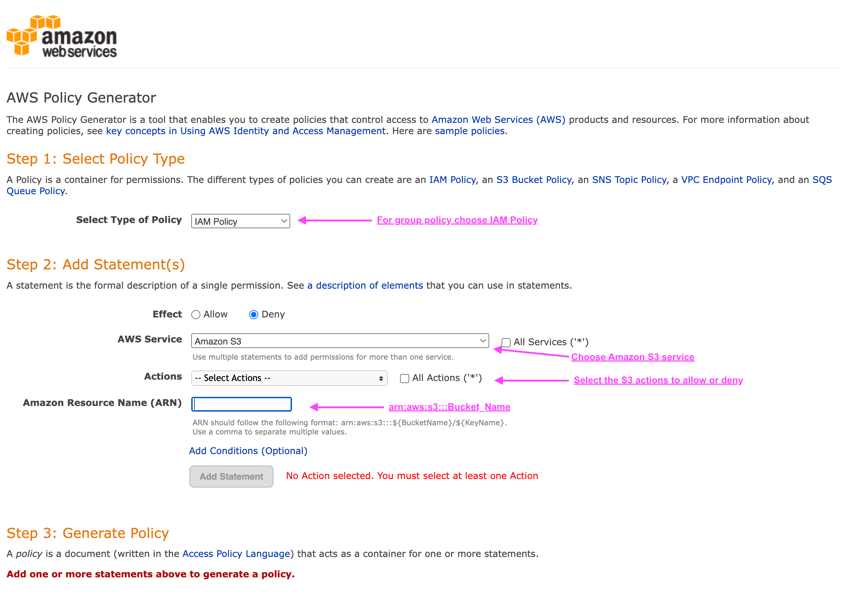
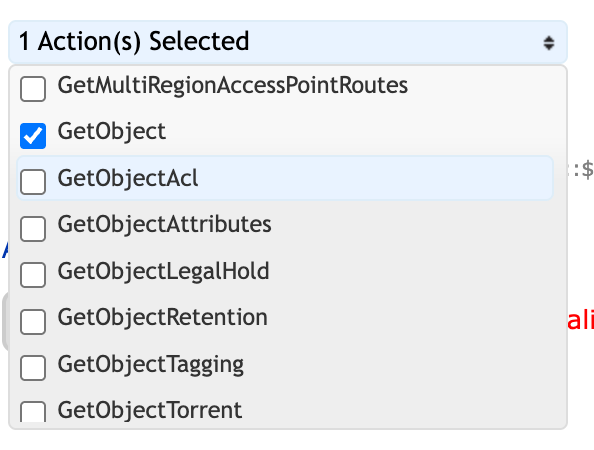
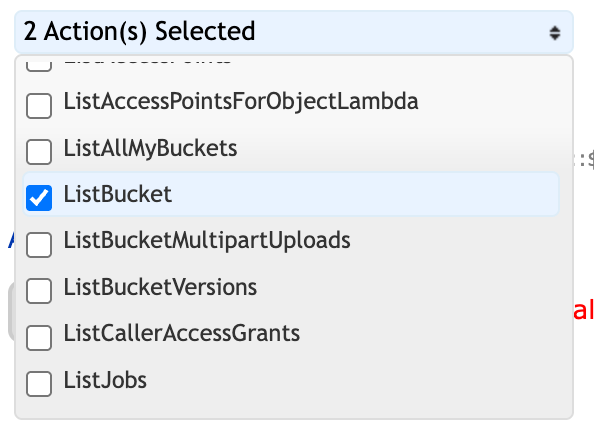
要为StorageGRID组策略生成权限、请执行以下操作:*为策略类型选择IAM策略。*选择所需效果的按钮-允许或拒绝。最好先使用拒绝权限启动策略、然后在操作下拉列表中添加允许权限*单击要包含在此权限中的尽可能多的S3操作旁边的框或"所有操作"框。*在Amazon资源名称(ARN)框中键入存储分段路径。在存储分段名称前包括"arn:aws:s3::::"。例如、"ARN:AWS:S3::::exple_bket"
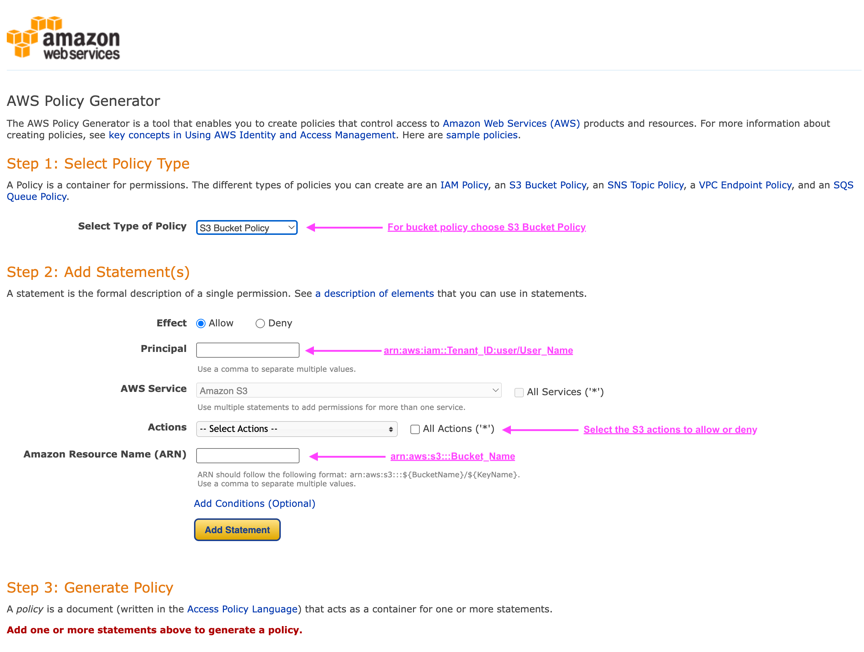
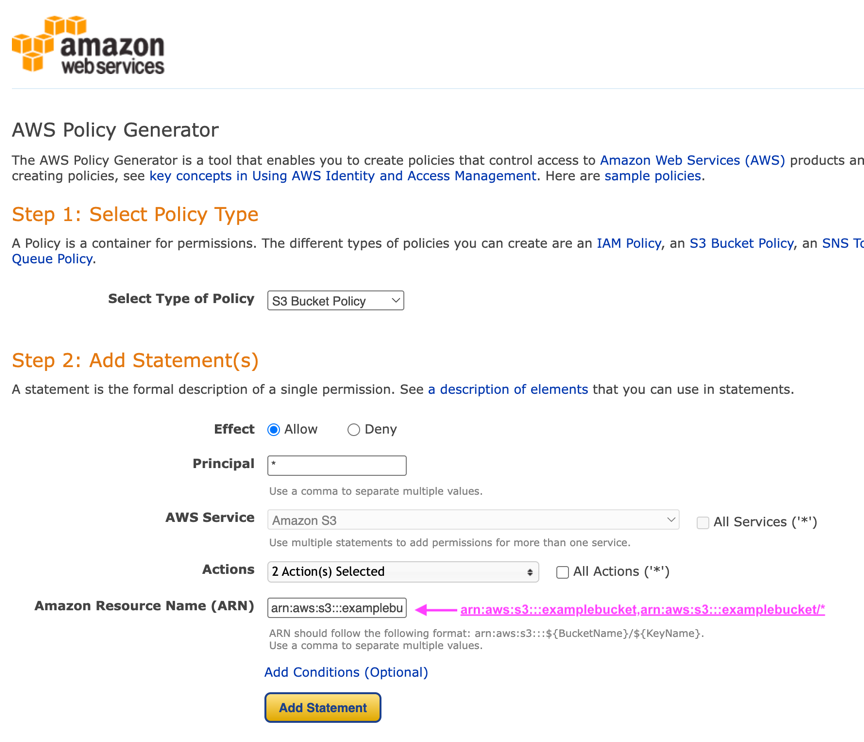
要为存储分段策略生成权限、请执行以下操作:*为策略类型选择S3存储分段策略。*选择所需效果的按钮-允许或拒绝。最好先使用拒绝权限启动策略、然后在主体的用户或组信息中添加允许权限*键入。*在操作下拉列表中、单击要包含在此权限中的S3操作旁边的框或"所有操作"框。*在Amazon资源名称(ARN)框中键入存储分段路径。在存储分段名称前包括"arn:aws:s3::::"。例如、"ARN:AWS:S3::::exple_bket"
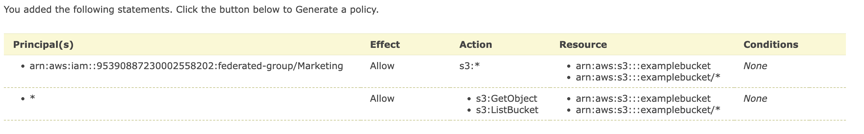
例如、如果要生成存储分段策略、以允许所有用户对存储分段中的所有对象执行GetObject操作、而仅允许指定帐户中属于组"Marketing"的用户进行完全访问。
-
选择S3存储分段策略作为策略类型。
-
选择允许效果
-
输入Marketing组信息:arn:aws:iam::95390887230002558202:联合组/营销
-
单击"所有操作"框
-
输入存储分段信息—arn:aws:s3::::exple_bket,arn:aws:s3::::exple_bket/*
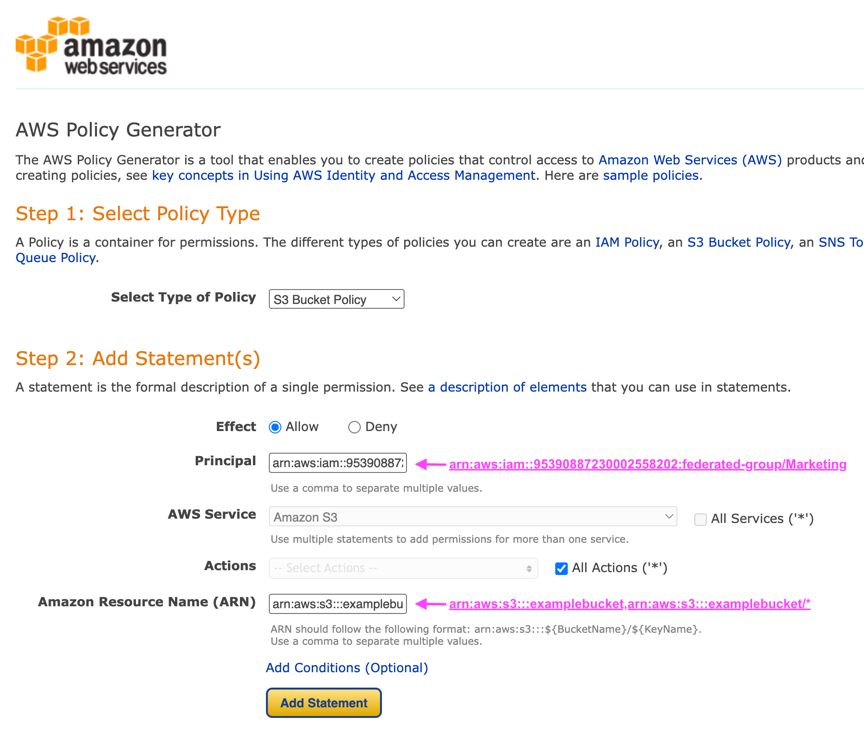
-
单击"Add Statement"(添加诊断代码)按钮
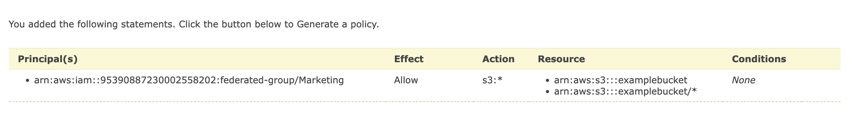
-
选择允许效果
-
为每个人输入星号*
-
单击GetObject和ListBucket"旁边的框
-
输入存储分段信息—arn:aws:s3::::exple_bket,arn:aws:s3::::exple_bket/*
-
单击"Add Statement"(添加诊断代码)按钮
-
单击"生成策略"按钮、此时将显示一个弹出窗口、其中会显示您生成的策略。

-
复制完整的json文本、如下所示:
{
"Id": "Policy1744399292233",
"Version": "2012-10-17",
"Statement": [
{
"Sid": "Stmt1744399152830",
"Action": "s3:*",
"Effect": "Allow",
"Resource": [
"arn:aws:s3:::example_bucket",
"arn:aws:s3:::example_bucket/*"
],
"Principal": {
"AWS": [
"arn:aws:iam::95390887230002558202:federated-group/Marketing"
]
}
},
{
"Sid": "Stmt1744399280838",
"Action": [
"s3:GetObject",
"s3:ListBucket"
],
"Effect": "Allow",
"Resource": [
"arn:aws:s3:::example_bucket",
"arn:aws:s3:::example_bucket/*"
],
"Principal": "*"
}
]
}此json可以按原样使用、也可以删除"Statement"行上方的ID和版本行、您可以自定义每个权限的Sid、并为每个权限指定更有意义的标题、也可以删除这些内容。
例如:
{
"Statement": [
{
"Sid": "MarketingAllowFull",
"Action": "s3:*",
"Effect": "Allow",
"Resource": [
"arn:aws:s3:::example_bucket",
"arn:aws:s3:::example_bucket/*"
],
"Principal": {
"AWS": [
"arn:aws:iam::95390887230002558202:federated-group/Marketing"
]
}
},
{
"Sid": "EveryoneReadOnly",
"Action": [
"s3:GetObject",
"s3:ListBucket"
],
"Effect": "Allow",
"Resource": [
"arn:aws:s3:::example_bucket",
"arn:aws:s3:::example_bucket/*"
],
"Principal": "*"
}
]
}组策略(IAM)
主目录模式的存储分段访问
此组策略仅允许用户访问名为Users username的分段中的对象。
{
"Statement": [
{
"Sid": "AllowListBucketOfASpecificUserPrefix",
"Effect": "Allow",
"Action": "s3:ListBucket",
"Resource": "arn:aws:s3:::home",
"Condition": {
"StringLike": {
"s3:prefix": "${aws:username}/*"
}
}
},
{
"Sid": "AllowUserSpecificActionsOnlyInTheSpecificUserPrefix",
"Effect": "Allow",
"Action": "s3:*Object",
"Resource": "arn:aws:s3:::home/?/?/${aws:username}/*"
}
]
}拒绝创建对象锁定分段
此组策略将限制用户创建在存储分段上启用了对象锁定的存储分段。

|
此策略不会在StorageGRID UI中强制实施、而是仅通过S3 API强制实施。 |
{
"Statement": [
{
"Action": "s3:*",
"Effect": "Allow",
"Resource": "arn:aws:s3:::*"
},
{
"Action": [
"s3:PutBucketObjectLockConfiguration",
"s3:PutBucketVersioning"
],
"Effect": "Deny",
"Resource": "arn:aws:s3:::*"
}
]
}对象锁定保留限制
此存储分段策略会将对象锁定保留期限限制为10天或更短
{
"Version":"2012-10-17",
"Id":"CustSetRetentionLimits",
"Statement": [
{
"Sid":"CustSetRetentionPeriod",
"Effect":"Deny",
"Principal":"*",
"Action": [
"s3:PutObjectRetention"
],
"Resource":"arn:aws:s3:::testlock-01/*",
"Condition": {
"NumericGreaterThan": {
"s3:object-lock-remaining-retention-days":"10"
}
}
}
]
}按版本ID限制用户删除对象
此组策略将限制用户按版本ID删除受版本控制的对象
{
"Statement": [
{
"Action": [
"s3:DeleteObjectVersion"
],
"Effect": "Deny",
"Resource": "arn:aws:s3:::*"
},
{
"Action": "s3:*",
"Effect": "Allow",
"Resource": "arn:aws:s3:::*"
}
]
}将组限制为具有只读访问权限的单个子目录(前缀)
此策略允许组成员对分段中的子目录(前缀)具有只读访问权限。分段名称为"study"、子目录为"study01"。
{
"Statement": [
{
"Sid": "AllowUserToSeeBucketListInTheConsole",
"Action": [
"s3:ListAllMyBuckets"
],
"Effect": "Allow",
"Resource": [
"arn:aws:s3:::*"
]
},
{
"Sid": "AllowRootAndstudyListingOfBucket",
"Action": [
"s3:ListBucket"
],
"Effect": "Allow",
"Resource": [
"arn:aws:s3::: study"
],
"Condition": {
"StringEquals": {
"s3:prefix": [
"",
"study01/"
],
"s3:delimiter": [
"/"
]
}
}
},
{
"Sid": "AllowListingOfstudy01",
"Action": [
"s3:ListBucket"
],
"Effect": "Allow",
"Resource": [
"arn:aws:s3:::study"
],
"Condition": {
"StringLike": {
"s3:prefix": [
"study01/*"
]
}
}
},
{
"Sid": "AllowAllS3ActionsInstudy01Folder",
"Effect": "Allow",
"Action": [
"s3:Getobject"
],
"Resource": [
"arn:aws:s3:::study/study01/*"
]
}
]
}存储分段策略
将存储分段限制为具有只读访问权限的单个用户
此策略允许单个用户对某个存储分段拥有只读访问权限、并明确授予所有其他用户的访问权限。将deny语句分组在策略顶部是一种较好的做法、可以加快评估速度。
{
"Statement": [
{
"Sid": "Deny non user1",
"Effect": "Deny",
"NotPrincipal": {
"AWS": "arn:aws:iam::34921514133002833665:user/user1"
},
"Action": [
"s3:*"
],
"Resource": [
"arn:aws:s3:::bucket1",
"arn:aws:s3:::bucket1/*"
]
},
{
"Sid": "Allow user1 read access to bucket bucket1",
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::34921514133002833665:user/user1"
},
"Action": [
"s3:GetObject",
"s3:ListBucket"
],
"Resource": [
"arn:aws:s3:::bucket1",
"arn:aws:s3:::bucket1/*"
]
}
]
}将存储分段限制为少数具有只读访问权限的用户。
{
"Statement": [
{
"Sid": "Deny all S3 actions to employees 002-005",
"Effect": "deny",
"Principal": {
"AWS": [
"arn:aws:iam::46521514133002703882:user/employee-002",
"arn:aws:iam::46521514133002703882:user/employee-003",
"arn:aws:iam::46521514133002703882:user/employee-004",
"arn:aws:iam::46521514133002703882:user/employee-005"
]
},
"Action": "*",
"Resource": [
"arn:aws:s3:::databucket1",
"arn:aws:s3:::databucket1/*"
]
},
{
"Sid": "Allow read-only access for employees 002-005",
"Effect": "Allow",
"Principal": {
"AWS": [
"arn:aws:iam::46521514133002703882:user/employee-002",
"arn:aws:iam::46521514133002703882:user/employee-003",
"arn:aws:iam::46521514133002703882:user/employee-004",
"arn:aws:iam::46521514133002703882:user/employee-005"
]
},
"Action": [
"s3:GetObject",
"s3:GetObjectTagging",
"s3:GetObjectVersion"
],
"Resource": [
"arn:aws:s3:::databucket1",
"arn:aws:s3:::databucket1/*"
]
}
]
}限制用户删除分段中受版本控制的对象
此存储分段策略将限制用户(由用户ID "56622399308951294926"标识)按版本ID删除版本控制的对象
{
"Statement": [
{
"Action": [
"s3:DeleteObjectVersion"
],
"Effect": "Deny",
"Resource": "arn:aws:s3:::verdeny/*",
"Principal": {
"AWS": [
"56622399308951294926"
]
}
},
{
"Action": "s3:*",
"Effect": "Allow",
"Resource": "arn:aws:s3:::verdeny/*",
"Principal": {
"AWS": [
"56622399308951294926"
]
}
}
]
}

