Networking overview for NetApp Copy and Sync
 Suggest changes
Suggest changes


Networking for NetApp Copy and Sync includes connectivity between the data broker group and the source and target locations, and an outbound internet connection from data brokers over port 443.
Data broker location
A data broker group consists of one or more data brokers installed in the cloud or on your premises.
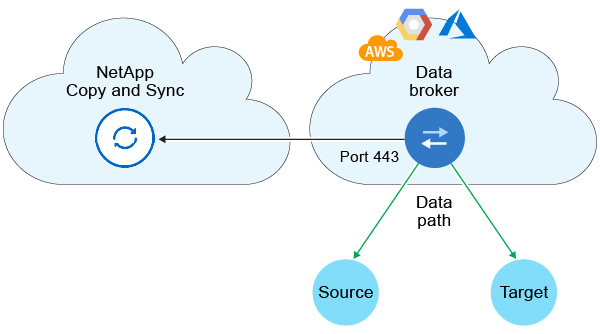
Data broker in the cloud
The following image shows a data broker running in the cloud, in either AWS, Google Cloud, or Azure. The source and target can be in any location, as long as there's a connection to the data broker. For example, you might have a VPN connection from your data center to your cloud provider.

|
When Copy and Sync deploys the data broker in AWS, Azure, or Google Cloud, it creates a security group that enables the required outbound communication. |
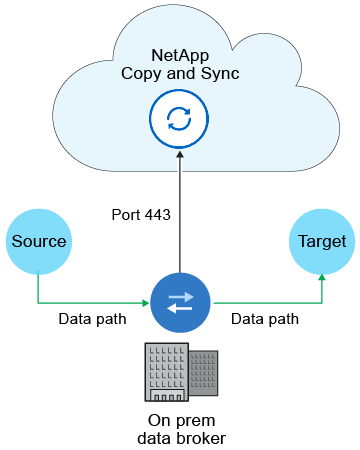
Data broker on your premises
The following image shows the data broker running on-premises in a data center. Again, the source and target can be in any location, as long as there's a connection to the data broker.
Networking requirements
-
The source and target must have a network connection to the data broker group.
For example, if an NFS server is in your data center and a data broker is in AWS, then you need a network connection (VPN or Direct Connect) from your network to the VPC.
-
A data broker needs an outbound internet connection so it can poll Copy and Sync for tasks over port 443.
-
NetApp recommends configuring the source, target, and data brokers to use a Network Time Protocol (NTP) service. The time difference between the three components should not exceed 5 minutes.
Networking endpoints
The NetApp data broker requires outbound internet access over port 443 to communicate with Copy and Sync and to contact a few other services and repositories. Your local web browser also requires access to endpoints for certain actions. If you need to limit outbound connectivity, refer to the following list of endpoints when configuring your firewall for outbound traffic.
Data broker endpoints
A data broker contacts the following endpoints:
| Endpoints | Purpose |
|---|---|
https://olcentgbl.trafficmanager.net |
To contact a repository for updating CentOS packages for the data broker host. This endpoint is contacted only if you manually install the data broker on a CentOS host. |
https://rpm.nodesource.com |
To contact repositories for updating Node.js, npm, and other 3rd party packages used in development. |
https://tgz.pm2.io |
To access a repository for updating PM2, which is a 3rd party package used to monitor Copy and Sync. |
https://sqs.us-east-1.amazonaws.com |
To contact the AWS services that Copy and Sync uses for operations (queuing files, registering actions, and delivering updates to the data broker). |
https://s3.region.amazonaws.com |
To contact Amazon S3 when a sync relationship includes an S3 bucket. |
https://s3.amazonaws.com/ |
When you download data broker logs from Copy and Sync, the data broker zips its logs directory and uploads the logs to a predefined S3 bucket in the us-east-1 region. |
https://storage.googleapis.com/ |
To contact Google Cloud when a sync relationship uses a GCP bucket. |
https://storage-account.blob.core.windows.net |
To open the proxy to a user's Azure storage account address. |
https://cf.cloudsync.netapp.com |
To contact Copy and Sync. |
https://support.netapp.com |
To contact NetApp support when using a BYOL license for sync relationships. |
https://fedoraproject.org |
To install 7z on the data broker virtual machine during installation and updates. 7z is needed to send AutoSupport messages to NetApp technical support. |
https://sts.amazonaws.com |
To verify AWS credentials when the data broker is deployed in AWS or when it's deployed on your premises and AWS credentials are provided. The data broker contacts this endpoint during deployment, when it's updated, and when it's restarted. |
https://api.bluexp.netapp.com |
To contact NetApp Data Classification when you use classification to select the source files for a new sync relationship. |
https://pubsub.googleapis.com |
If creating a continuous sync relationship from a Google storage account. |
https://storage-account.queue.core.windows.net |
If creating a continuous sync relationship from an Azure storage account. |
Web browser endpoints
Your web browser needs access to the following endpoint to download logs for troubleshooting purposes:
logs.cloudsync.netapp.com:443


