Configure protection settings in NetApp Ransomware Resilience
 Suggest changes
Suggest changes


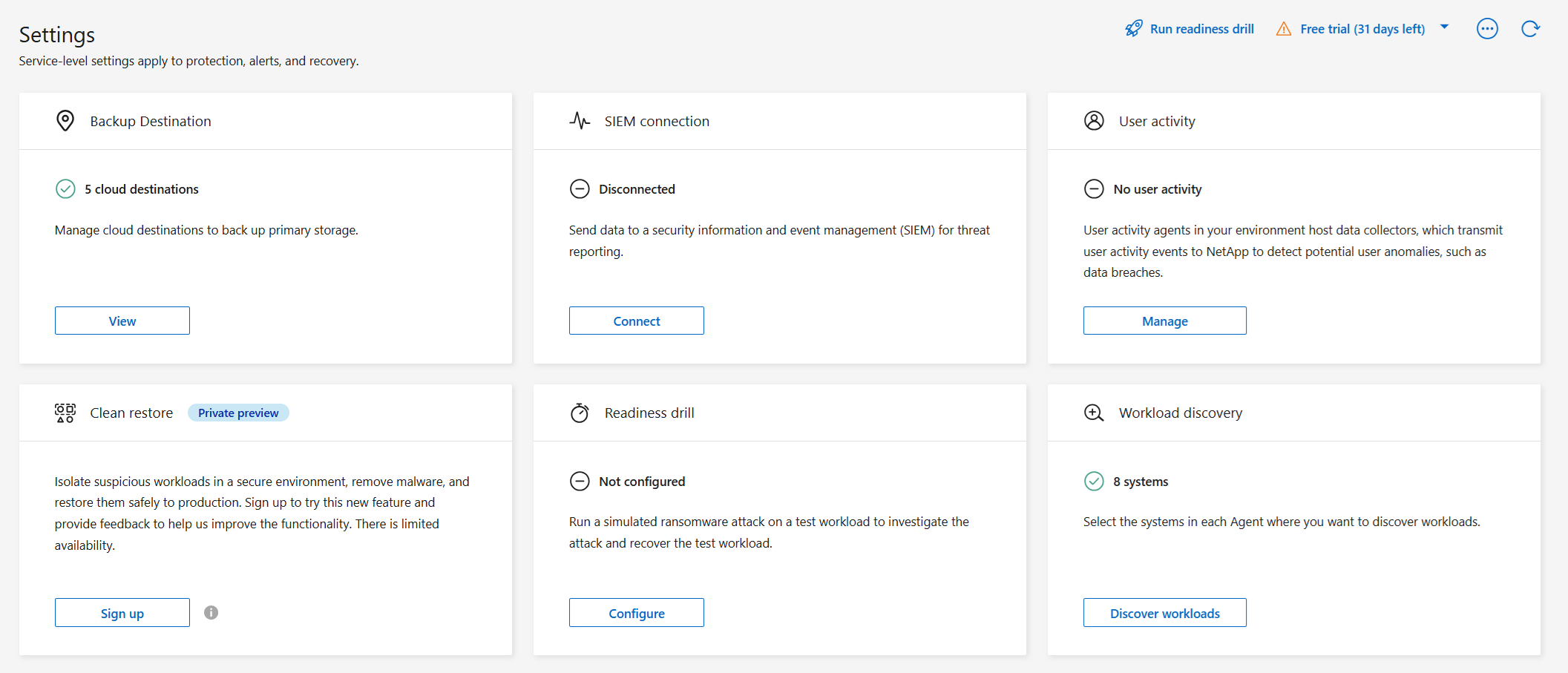
You can configure backup destinations, send data to an external security and event management (SIEM) system, conduct an attack readiness drill, configure workload discovery, or configure suspicious user activity detection by accessing the Settings option.
Required Console role
To perform this task, you need the Organization admin, Folder or project admin, or Ransomware Resilience admin role. Learn about Ransomware Resilience roles for NetApp Console.
What can you do in the Settings page?
From the Settings page, you can do the following:
-
Simulate a ransomware attack by conducting a readiness drill and respond to a simulated ransomware alert. For details, see Conduct a ransomware attack readiness drill.
-
Configure workload discovery.
-
Configure suspicious user activity reporting.
-
Add a backup destination.
-
Connect your security and event management system (SIEM) for threat analysis and detection. Enabling threat detection automatically sends data to your SIEM for threat analysis.
Access the Settings page directly
You can easily access the Settings page from the Actions option near the top menu.
-
From the Ransomware Resilience, select the vertical
 … option at the top right.
… option at the top right. -
From the drop-down menu, select Settings.
Simulate a ransomware attack
Conduct a ransomware readiness drill by simulating a ransomware attack on a newly created, sample workload. Then, investigate the simulated attack and recover the sample workload. This feature helps you know that you are prepared in the event of an actual ransomware attack by testing alert notification, response, and recovery processes. You can run a ransomware readiness drill multiple times.
For details, refer to Conduct a ransomware attack readiness drill.
Configure workload discovery
You can configure workload discovery to automatically discover new workloads in your environment.
-
In the Settings page, locate the Workload discovery tile.
-
In the Workload discovery tile, select Discover workloads.
This page shows Console agents with systems that were not selected earlier, newly available Console agents, and newly available systems. This page doesn't show those systems that were previously selected.
-
Select the Console agent where you want to discover workloads.
-
Review the list of systems.
-
Check the systems where you want to discover workloads or select the box at the top of the table to discover workloads in all discovered workload environments.
-
Do this for other systems as needed.
-
Select Discover to have Ransomware Resilience automatically discover new workloads in the selected Console agent.

|
From the Workload discovery card in Settings, select the action menu … then Download report (JSON) to review a list of supported and unsupported workloads in your systems.
|
Suspicious user activity
In the User activity card, you can create and manage the user activity agent that is required to detect suspicious user activity.
For more information, see Suspicious user activity.
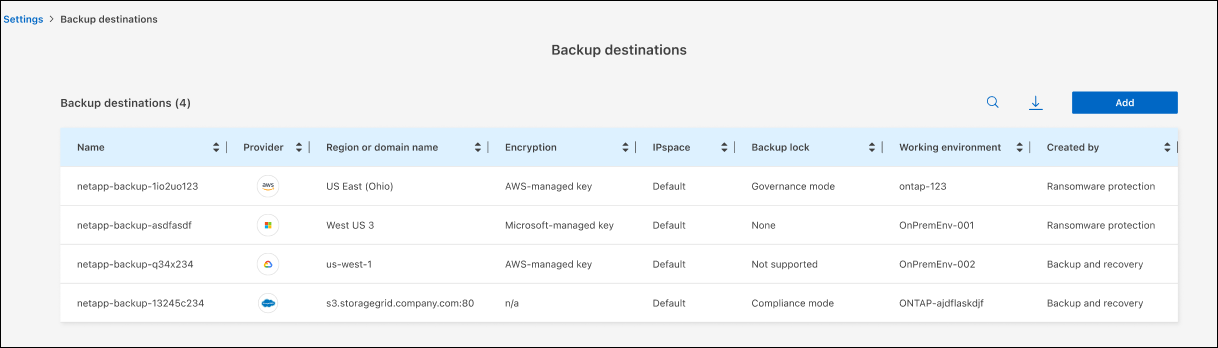
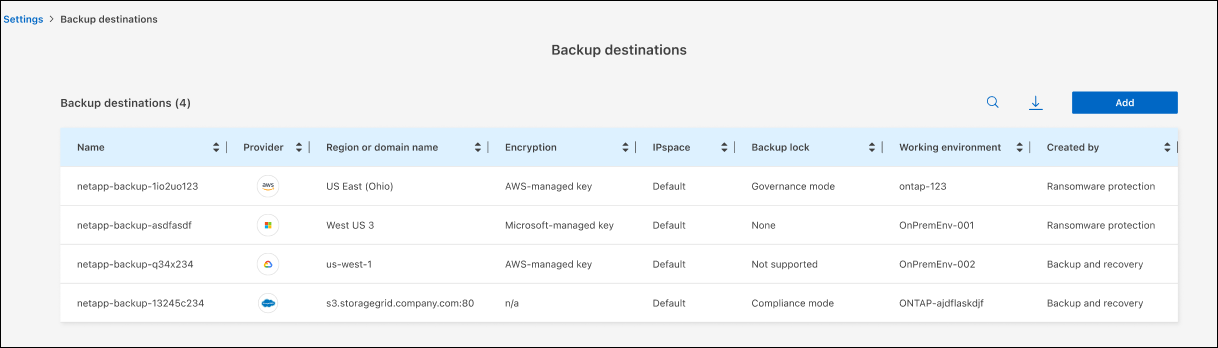
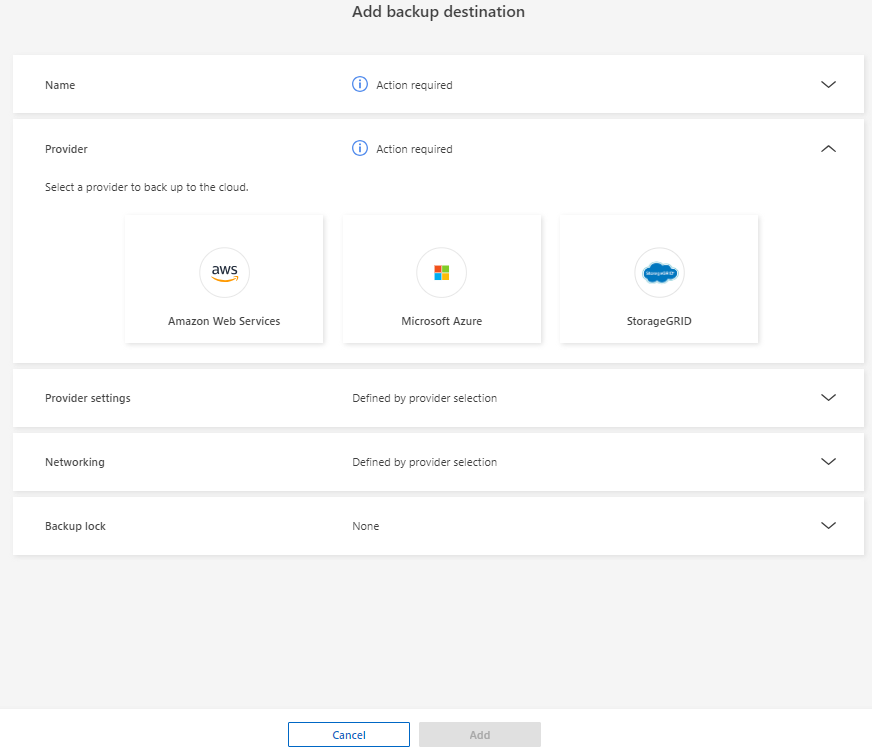
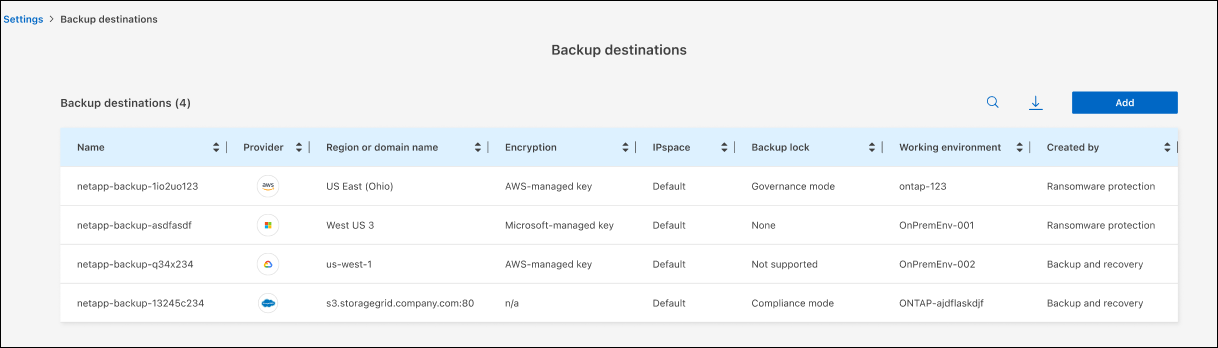
Add a backup destination
Ransomware Resilience can identify workloads that do not have any backups yet and also workloads that do not have any backup destinations assigned yet.
To protect those workloads, you should add a backup destination. You can choose one of the following backup destinations:
-
NetApp StorageGRID
-
Amazon Web Services (AWS)
-
Google Cloud Platform
-
Microsoft Azure

|
Backup destinations are not available for workloads in Amazon FSx for NetApp ONTAP. Perform backup operations using the FSx for ONTAP backup service. |
You can add a backup destination based on a recommended action from the Dashboard or from accessing the Settings option on the menu.
Access Backup Destination options from the Dashboard's recommended actions
The Dashboard provides many recommendations. One recommendation might be to configure a backup destination.
-
In the Ransomware Resilience dashboard, review the Recommended actions pane.
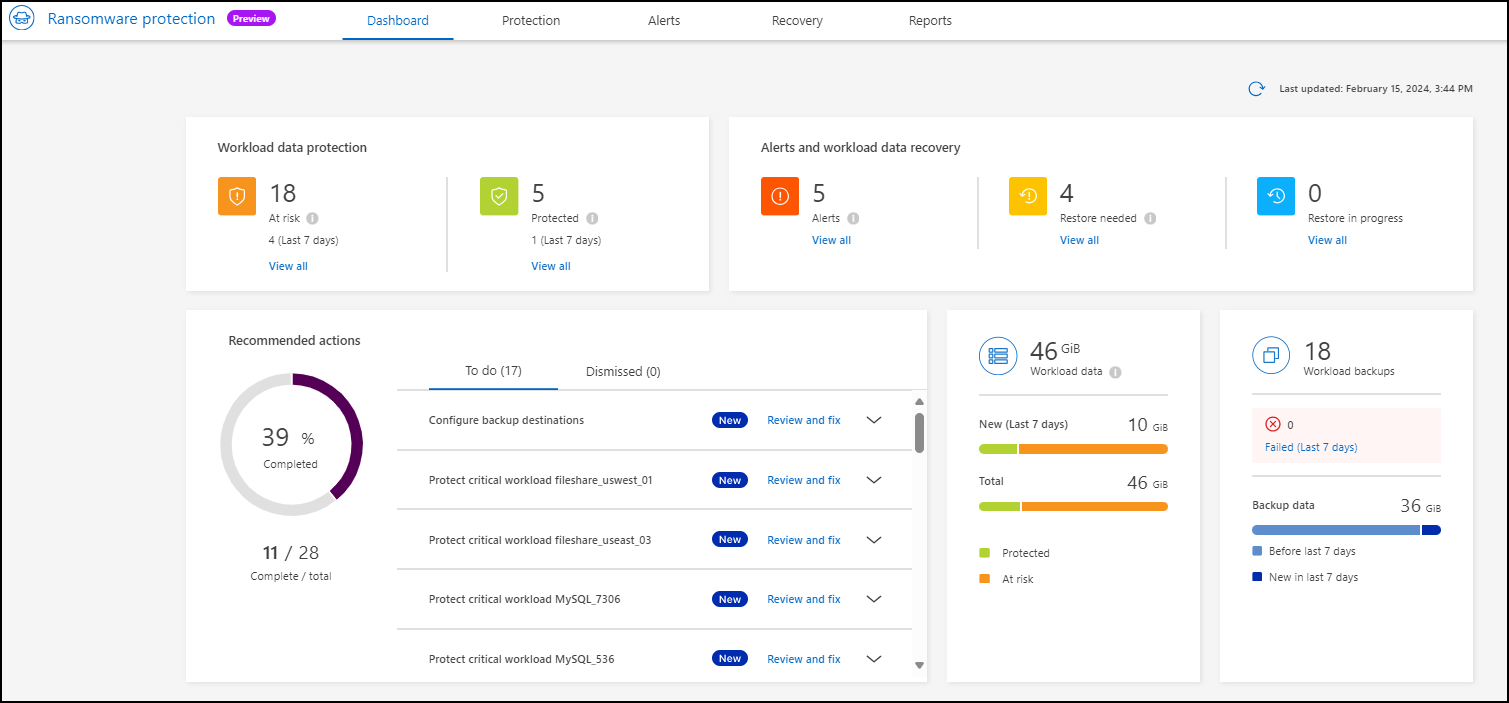
-
From the Dashboard, select Review and fix for the recommendation of "Prepare <backup provider> as a backup destination."
-
Continue with instructions depending on the backup provider.
Add StorageGRID as a backup destination
To set up NetApp StorageGRID as a backup destination, enter the following information.
-
In the Settings > Backup destinations page, select Add.
-
Enter a name for the backup destination.
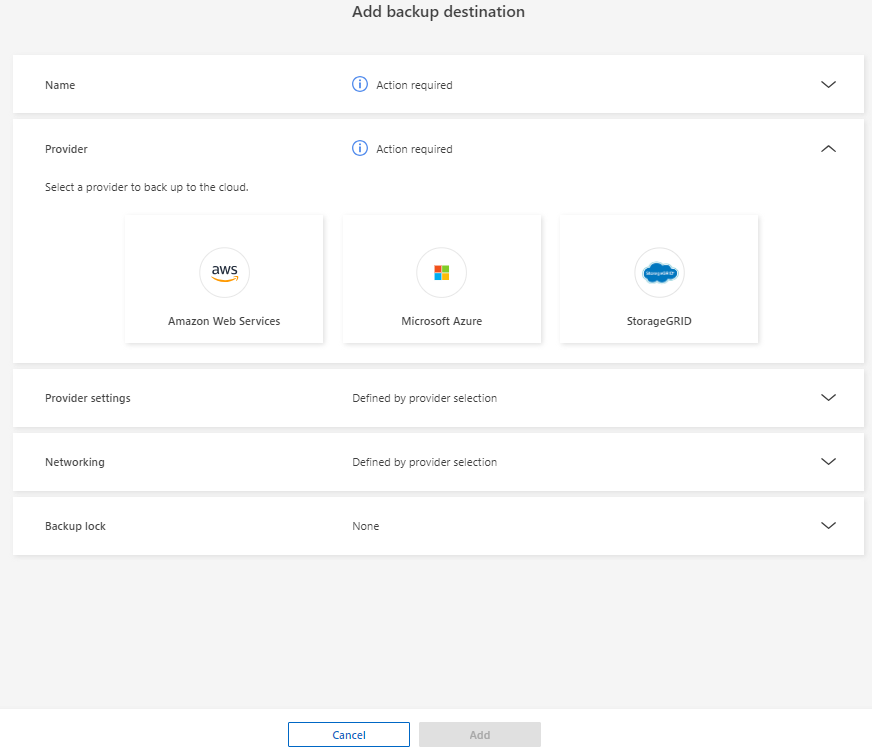
-
Select StorageGRID.
-
Select the down arrow next to each setting and enter or select values:
-
Provider settings:
-
Create a new bucket or bring your own bucket that will store the backups.
-
StorageGRID gateway node fully qualified domain name, port, StorageGRID access key and secret key credentials.
-
-
Networking: Choose the IPspace.
-
The IPspace is the cluster where the volumes you want to back up reside. The intercluster LIFs for this IPspace must have outbound internet access.
-
-
-
Select Add.
The new backup destination is added to the list of backup destinations.
Add Amazon Web Services as a backup destination
To set up AWS as a backup destination, enter the following information.
For details about managing your AWS storage in the Console, refer to Manage your Amazon S3 buckets.
-
In the Settings > Backup destinations page, select Add.
-
Enter a name for the backup destination.
-
Select Amazon Web Services.
-
Select the Down arrow next to each setting and enter or select values:
-
Provider settings:
-
Create a new bucket, select an existing bucket if one already exists in the Console, or bring your own bucket that will store the backups.
-
AWS account, region, access key and secret key for AWS credentials
-
-
Encryption: If you are creating a new S3 bucket, enter encryption key information given to you from the provider. If you chose an existing bucket, encryption information is already available.
Data in the bucket is encrypted with AWS-managed keys by default. You can continue to use AWS-managed keys, or you can manage the encryption of your data using your own keys.
-
Networking: Choose the IPspace and whether you'll be using a Private Endpoint.
-
The IPspace is the cluster where the volumes you want to back up reside. The intercluster LIFs for this IPspace must have outbound internet access.
-
Optionally, choose whether you'll use an AWS private endpoint (PrivateLink) that you previously configured.
If you want to use AWS PrivateLink, refer to AWS PrivateLink for Amazon S3.
-
-
Backup lock: Choose whether you want Ransomware Resilience to protect backups from being modified or deleted. This option uses the NetApp DataLock technology. Each backup will be locked during the retention period, or for a minimum of 30 days, plus a buffer period of up to 14 days.
If you configure the backup lock setting now, you cannot change the setting later after the backup destination is configured. -
Governance mode: Specific users (with s3:BypassGovernanceRetention permission) can overwrite or delete protected files during the retention period.
-
Compliance mode: Users cannot overwrite or delete protected backup files during the retention period.
-
-
-
Select Add.
The new backup destination is added to the list of backup destinations.
Add Google Cloud Platform as a backup destination
To set up Google Cloud Platform (GCP) as a backup destination, enter the following information.
For details about managing your GCP storage in the Console, refer to Console agent installation options in Google Cloud.
-
In the Settings > Backup destinations page, select Add.
-
Enter a name for the backup destination.
-
Select Google Cloud Platform.
-
Select the Down arrow next to each setting and enter or select values:
-
Provider settings:
-
Create a new bucket. Enter the access key and secret key.
-
Enter or select your Google Cloud Platform project and region.
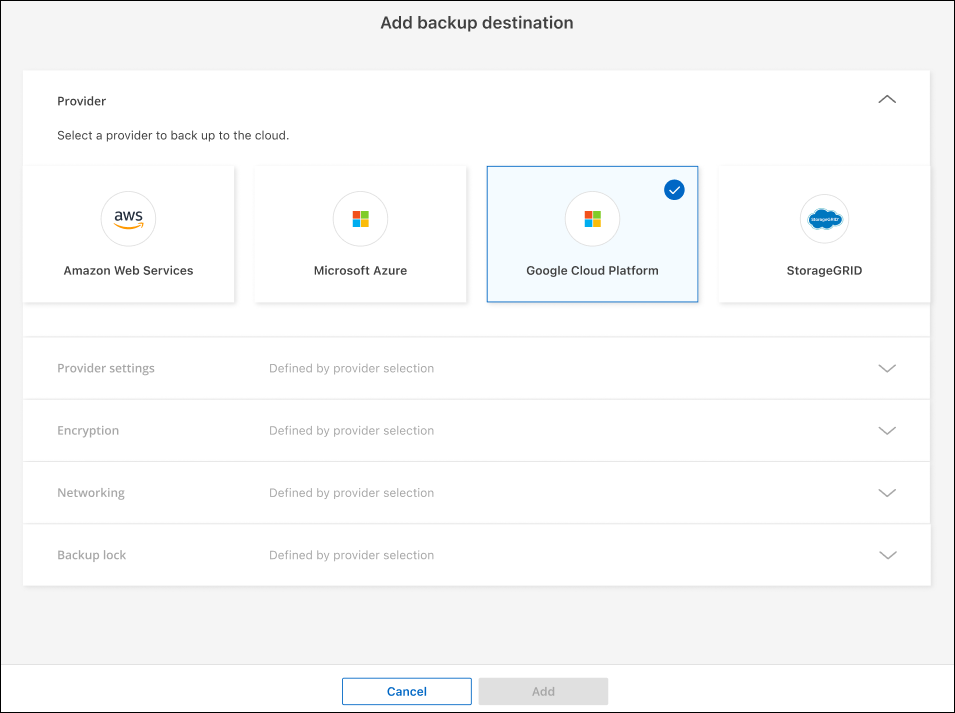
-
-
Encryption: If you are creating a new bucket, enter encryption key information given to you from the provider. If you chose an existing bucket, encryption information is already available.
Data in the bucket is encrypted with Google-managed keys by default. You can continue to use Google-managed keys.
-
Networking: Choose the IPspace and whether you'll be using a Private Endpoint.
-
The IPspace is the cluster where the volumes you want to back up reside. The intercluster LIFs for this IPspace must have outbound internet access.
-
Optionally, choose whether you'll use an GCP private endpoint (PrivateLink) that you previously configured.
-
-
-
Select Add.
The new backup destination is added to the list of backup destinations.
Add Microsoft Azure as a backup destination
To set up Azure as a backup destination, enter the following information.
For details about managing your Azure credentials and marketplace subscriptions in the Console, refer to Manage your Azure credentials and marketplace subscriptions.
-
In the Settings > Backup destinations page, select Add.
-
Enter a name for the backup destination.
-
Select Azure.
-
Select the Down arrow next to each setting and enter or select values:
-
Provider settings:
-
Create a new storage account, select an existing one if one already exists in the Console, or bring your own storage account that will store the backups.
-
Azure subscription, region, and resource group for Azure credentials
-
-
Encryption: If you are creating a new storage account, enter encryption key information given to you from the provider. If you chose an existing account, encryption information is already available.
Data in the account is encrypted with Microsoft-managed keys by default. You can continue to use Microsoft-managed keys, or you can manage the encryption of your data using your own keys.
-
Networking: Choose the IPspace and whether you'll be using a Private Endpoint.
-
The IPspace is the cluster where the volumes you want to back up reside. The intercluster LIFs for this IPspace must have outbound internet access.
-
Optionally, choose whether you'll use an Azure private endpoint that you previously configured.
If you want to use Azure PrivateLink, refer to Azure PrivateLink.
-
-
-
Select Add.
The new backup destination is added to the list of backup destinations.
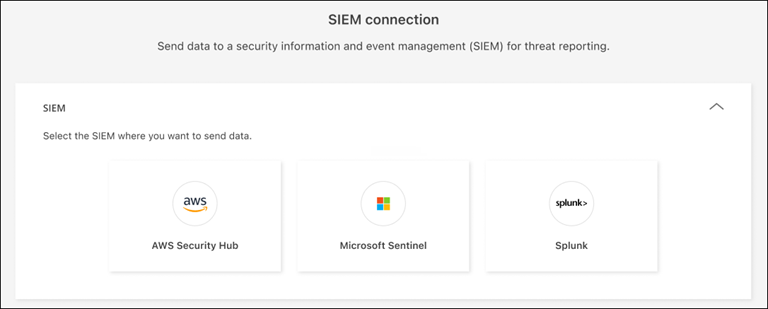
Connect to a security and event management system (SIEM) for threat analysis and detection
You can automatically send data to your security and event management system (SIEM) for threat analysis and detection. You can select the AWS Security Hub, Microsoft Sentinel, or Splunk Cloud as your SIEM.
Before you enable SIEM in Ransomware Resilience, you need to configure your SIEM system.
Ransomware Resilience can send the following event data to your SIEM system:
-
context:
-
os: This is a constant with the value of ONTAP.
-
os_version: The version of ONTAP running on the system.
-
connector_id: The ID of the Console agent managing the system.
-
cluster_id: The cluster ID reported by ONTAP for the system.
-
svm_name: The name of the SVM where the alert was found.
-
volume_name: The name of the volume on which the alert is found.
-
volume_id: The ID of the volume reported by ONTAP for the system.
-
-
incident:
-
incident_id: The incident ID generated by Ransomware Resilience for the volume under attack in Ransomware Resilience.
-
alert_id: The ID generated by Ransomware Resilience for the workload.
-
severity: One of the following alert levels: "CRITICAL", "HIGH", "MEDIUM", "LOW".
-
description: Details about the alert that was detected, for example, "A Potential ransomware attack detected on workload arp_learning_mode_test_2630"
-
Configure AWS Security Hub for threat detection
Before you enable AWS Security Hub in Ransomware Resilience, you'll need to do the following high level steps in AWS Security Hub:
-
Set up permissions in AWS Security Hub.
-
Set up the authentication access key and secret key in AWS Security Hub. (These steps are not provided here.)
-
Go to AWS IAM console.
-
Select Policies.
-
Create a policy using the following code in JSON format:
{ "Version": "2012-10-17", "Statement": [ { "Sid": "NetAppSecurityHubFindings", "Effect": "Allow", "Action": [ "securityhub:BatchImportFindings", "securityhub:BatchUpdateFindings" ], "Resource": [ "arn:aws:securityhub:*:*:product/*/default", "arn:aws:securityhub:*:*:hub/default" ] } ] }
Configure Microsoft Sentinel for threat detection
Before you enable Microsoft Sentinel in Ransomware Resilience, you'll need to do the following high level steps in Microsoft Sentinel:
-
Prerequisites
-
Enable Microsoft Sentinel.
-
Create a custom role in Microsoft Sentinel.
-
-
Registration
-
Register Ransomware Resilience to receive events from Microsoft Sentinel.
-
Create a secret for the registration.
-
-
Permissions: Assign permissions to the application.
-
Authentication: Enter authentication credentials for the application.
-
Go to Microsoft Sentinel.
-
Create a Log Analytics workspace.
-
Enable Microsoft Sentinel to use the Log Analytics workspace you just created.
-
Go to Microsoft Sentinel.
-
Select Subscription > Access control (IAM).
-
Enter a Custom role name. Use the name Ransomware Resilience Sentinel Configurator.
-
Copy the following JSON and paste it into the JSON tab.
{ "roleName": "Ransomware Resilience Sentinel Configurator", "description": "", "assignableScopes":["/subscriptions/{subscription_id}"], "permissions": [ ] } -
Review and save your settings.
-
Go to Microsoft Sentinel.
-
Select Entra ID > Applications > App registrations.
-
For the Display name for the application, enter "Ransomware Resilience".
-
In the Supported account type field, select Accounts in this organizational directory only.
-
Select a Default Index where events will be pushed.
-
Select Review.
-
Select Register to save your settings.
After registration, the Microsoft Entra admin center displays the application Overview pane.
-
Go to Microsoft Sentinel.
-
Select Certificates & secrets > Client secrets > New client secret.
-
Add a description for your application secret.
-
Select an Expiration for the secret or specify a custom lifetime.
A client secret lifetime is limited to two years (24 months) or less. Microsoft recommends that you set an expiration value of less than 12 months. -
Select Add to create your secret.
-
Record the secret to use in the Authentication step. The secret is never displayed again after you leave this page.
-
Go to Microsoft Sentinel.
-
Select Subscription > Access control (IAM).
-
Select Add > Add role assignment.
-
For the Privileged administrator roles field, select Ransomware Resilience Sentinel Configurator.
This is the custom role that you created earlier. -
Select Next.
-
In the Assign access to field, select User, group, or service principal.
-
Select Select Members. Then, select Ransomware Resilience Sentinel Configurator.
-
Select Next.
-
In the What user can do field, select Allow user to assign all roles except privileged administrator roles Owner, UAA, RBAC (Recommended).
-
Select Next.
-
Select Review and assign to assign the permissions.
-
Go to Microsoft Sentinel.
-
Enter the credentials:
-
Enter the tenant ID, the client application ID, and the client application secret.
-
Click Authenticate.
After the authentication is successful, an "Authenticated" message appears.
-
-
Enter the Log Analytics workspace details for the application.
-
Select the subscription ID, the resource group, and the Log Analytics workspace.
-
Configure Splunk Cloud for threat detection
Before you enable Splunk Cloud in Ransomware Resilience, you'll need to do the following high level steps in Splunk Cloud:
-
Enable an HTTP Event Collector in Splunk Cloud to receive event data via HTTP or HTTPS from the Console.
-
Create an Event Collector token in Splunk Cloud.
-
Go to Splunk Cloud.
-
Select Settings > Data Inputs.
-
Select HTTP Event Collector > Global Settings.
-
On the All Tokens toggle, select Enabled.
-
To have the Event Collector listen and communicate over HTTPS rather than HTTP, select Enable SSL.
-
Enter a port in HTTP Port Number for the HTTP Event Collector.
-
Go to Splunk Cloud.
-
Select Settings > Add Data.
-
Select Monitor > HTTP Event Collector.
-
Enter a Name for the token and select Next.
-
Select a Default Index where events will be pushed, then select Review.
-
Confirm that all settings for the endpoint are correct, then select Submit.
-
Copy the token and paste it in another document to have it ready for the Authentication step.
Connect SIEM in Ransomware Resilience
Enabling SIEM sends data from Ransomware Resilience to your SIEM server for threat analysis and reporting.
-
From the Console menu, select Protection > Ransomware Resilience.
-
From the Ransomware Resilience menu, select the vertical
 … option at the top right.
… option at the top right. -
Select Settings.
The Settings page appears.
-
In the Settings page, select Connect in the SIEM connection tile.
-
Choose one of the SIEM systems.
-
Enter the token and authentication details you configured in AWS Security Hub or Splunk Cloud.
The information that you enter depends on the SIEM you selected. -
Select Enable.
The Settings page shows "Connected."



