Use identity federation
 Suggest changes
Suggest changes


Using identity federation makes setting up tenant groups and users faster, and it allows tenant users to sign in to the tenant account using familiar credentials.
Configure identity federation for Tenant Manager
You can configure identity federation for the Tenant Manager if you want tenant groups and users to be managed in another system such as Active Directory, Azure Active Directory (Azure AD), OpenLDAP, or Oracle Directory Server.
-
You are signed in to the Tenant Manager using a supported web browser.
-
You have specific access permissions.
-
You are using Active Directory, Azure AD, OpenLDAP, or Oracle Directory Server as the identity provider.
If you want to use an LDAP v3 service that is not listed, contact technical support. -
If you plan to use OpenLDAP, you must configure the OpenLDAP server. See Guidelines for configuring OpenLDAP server.
-
If you plan to use Transport Layer Security (TLS) for communications with the LDAP server, the identity provider must be using TLS 1.2 or 1.3. See Supported ciphers for outgoing TLS connections.
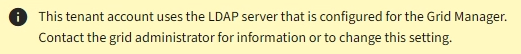
Whether you can configure an identity federation service for your tenant depends on how your tenant account was set up. Your tenant might share the identity federation service that was configured for the Grid Manager. If you see this message when you access the Identity Federation page, you cannot configure a separate federated identity source for this tenant.
Enter configuration
-
Select ACCESS MANAGEMENT > Identity federation.
-
Select Enable identity federation.
-
In the LDAP service type section, select the type of LDAP service you want to configure.
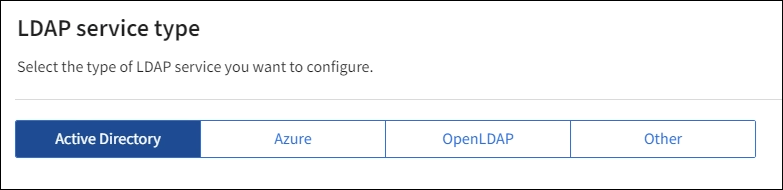
Select Other to configure values for an LDAP server that uses Oracle Directory Server.
-
If you selected Other, complete the fields in the LDAP Attributes section. Otherwise, go to the next step.
-
User Unique Name: The name of the attribute that contains the unique identifier of an LDAP user. This attribute is equivalent to
sAMAccountNamefor Active Directory anduidfor OpenLDAP. If you are configuring Oracle Directory Server, enteruid. -
User UUID: The name of the attribute that contains the permanent unique identifier of an LDAP user. This attribute is equivalent to
objectGUIDfor Active Directory andentryUUIDfor OpenLDAP. If you are configuring Oracle Directory Server, enternsuniqueid. Each user's value for the specified attribute must be a 32-digit hexadecimal number in either 16-byte or string format, where hyphens are ignored. -
Group Unique Name: The name of the attribute that contains the unique identifier of an LDAP group. This attribute is equivalent to
sAMAccountNamefor Active Directory andcnfor OpenLDAP. If you are configuring Oracle Directory Server, entercn. -
Group UUID: The name of the attribute that contains the permanent unique identifier of an LDAP group. This attribute is equivalent to
objectGUIDfor Active Directory andentryUUIDfor OpenLDAP. If you are configuring Oracle Directory Server, enternsuniqueid. Each group's value for the specified attribute must be a 32-digit hexadecimal number in either 16-byte or string format, where hyphens are ignored.
-
-
For all LDAP service types, enter the required LDAP server and network connection information in the Configure LDAP server section.
-
Hostname: The fully qualified domain name (FQDN) or IP address of the LDAP server.
-
Port: The port used to connect to the LDAP server.
The default port for STARTTLS is 389, and the default port for LDAPS is 636. However, you can use any port as long as your firewall is configured correctly. -
Username: The full path of the distinguished name (DN) for the user that will connect to the LDAP server.
For Active Directory, you can also specify the Down-Level Logon Name or the User Principal Name.
The specified user must have permission to list groups and users and to access the following attributes:
-
sAMAccountNameoruid -
objectGUID,entryUUID, ornsuniqueid -
cn -
memberOforisMemberOf -
Active Directory:
objectSid,primaryGroupID,userAccountControl, anduserPrincipalName -
Azure:
accountEnabledanduserPrincipalName
-
-
Password: The password associated with the username.
-
Group Base DN: The full path of the distinguished name (DN) for an LDAP subtree you want to search for groups. In the Active Directory example (below), all groups whose Distinguished Name is relative to the base DN (DC=storagegrid,DC=example,DC=com) can be used as federated groups.
The Group unique name values must be unique within the Group Base DN they belong to. -
User Base DN: The full path of the distinguished name (DN) of an LDAP subtree you want to search for users.
The User unique name values must be unique within the User Base DN they belong to. -
Bind username format (optional): The default username pattern StorageGRID should use if the pattern cannot be determined automatically.
Providing Bind username format is recommended because it can allow users to sign in if StorageGRID is unable to bind with the service account.
Enter one of these patterns:
-
UserPrincipalName pattern (Active Directory and Azure):
[USERNAME]@example.com -
Down-level logon name pattern (Active Directory and Azure):
example\[USERNAME] -
Distinguished name pattern:
CN=[USERNAME],CN=Users,DC=example,DC=comInclude [USERNAME] exactly as written.
-
-
-
In the Transport Layer Security (TLS) section, select a security setting.
-
Use STARTTLS: Use STARTTLS to secure communications with the LDAP server. This is the recommended option for Active Directory, OpenLDAP, or Other, but this option is not supported for Azure.
-
Use LDAPS: The LDAPS (LDAP over SSL) option uses TLS to establish a connection to the LDAP server. You must select this option for Azure.
-
Do not use TLS: The network traffic between the StorageGRID system and the LDAP server will not be secured. This option is not supported for Azure.
Using the Do not use TLS option is not supported if your Active Directory server enforces LDAP signing. You must use STARTTLS or LDAPS.
-
-
If you selected STARTTLS or LDAPS, choose the certificate used to secure the connection.
-
Use operating system CA certificate: Use the default Grid CA certificate installed on the operating system to secure connections.
-
Use custom CA certificate: Use a custom security certificate.
If you select this setting, copy and paste the custom security certificate into the CA certificate text box.
-
Test the connection and save the configuration
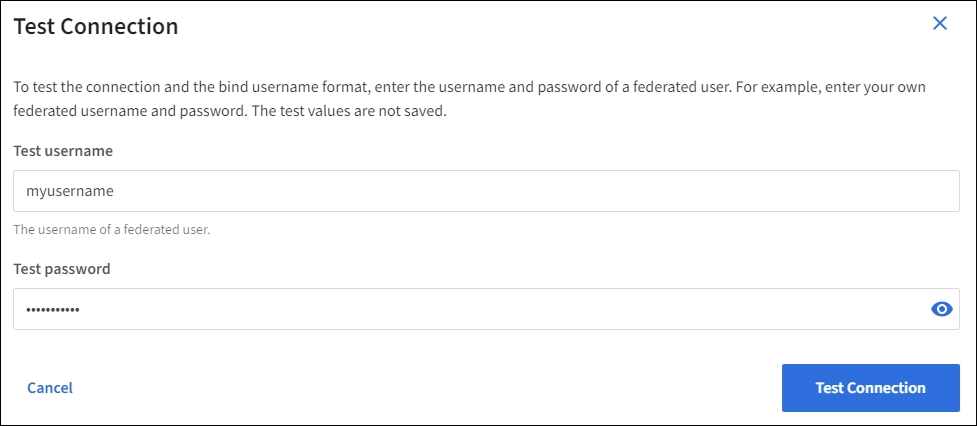
After entering all values, you must test the connection before you can save the configuration. StorageGRID verifies the connection settings for the LDAP server and the bind username format, if you provided one.
-
Select Test connection.
-
If you did not provide a bind username format:
-
A “Test connection successful” message appears if the connection settings are valid. Select Save to save the configuration.
-
A “test connection could not be established” message appears if the connection settings are invalid. Select Close. Then, resolve any issues and test the connection again.
-
-
If you provided a bind username format, enter the username and password of a valid federated user.
For example, enter your own username and password. Do not include any special characters in the username, such as @ or /.
-
A “Test connection successful” message appears if the connection settings are valid. Select Save to save the configuration.
-
An error message appears if the connection settings, bind username format, or test username and password are invalid. Resolve any issues and test the connection again.
-
Force synchronization with identity source
The StorageGRID system periodically synchronizes federated groups and users from the identity source. You can force synchronization to start if you want to enable or restrict user permissions as quickly as possible.
-
Go to the Identity federation page.
-
Select Sync server at the top of the page.
The synchronization process might take some time depending on your environment.
The Identity federation synchronization failure alert is triggered if there is an issue synchronizing federated groups and users from the identity source.
Disable identity federation
You can temporarily or permanently disable identity federation for groups and users. When identity federation is disabled, there is no communication between StorageGRID and the identity source. However, any settings you have configured are retained, allowing you to easily reenable identity federation in the future.
Before you disable identity federation, you should be aware of the following:
-
Federated users will be unable to sign in.
-
Federated users who are currently signed in will retain access to the StorageGRID system until their session expires, but they will be unable to sign in after their session expires.
-
Synchronization between the StorageGRID system and the identity source will not occur, and alerts or alarms will not be raised for accounts that have not been synchronized.
-
The Enable identity federation check box is disabled if single sign-on (SSO) is set to Enabled or Sandbox Mode. The SSO Status on the Single Sign-on page must be Disabled before you can disable identity federation. See Disable single sign-on.
-
Go to the Identity federation page.
-
Uncheck the Enable identity federation check box.
Guidelines for configuring OpenLDAP server
If you want to use an OpenLDAP server for identity federation, you must configure specific settings on the OpenLDAP server.

|
For identity sources that are not ActiveDirectory or Azure, StorageGRID will not automatically block S3 access to users who are disabled externally. To block S3 access, delete any S3 keys for the user and remove the user from all groups. |
Memberof and refint overlays
The memberof and refint overlays should be enabled. For more information, see the instructions for reverse group membership maintenance in the OpenLDAP documentation: Version 2.4 Administrator's Guide.
Indexing
You must configure the following OpenLDAP attributes with the specified index keywords:
-
olcDbIndex: objectClass eq -
olcDbIndex: uid eq,pres,sub -
olcDbIndex: cn eq,pres,sub -
olcDbIndex: entryUUID eq
In addition, ensure the fields mentioned in the help for Username are indexed for optimal performance.
See the information about reverse group membership maintenance in the OpenLDAP documentation: Version 2.4 Administrator's Guide.



